Securing a specific phone number so that only authorized callers can reach the destination is a common request in modern telecommunications. But how do you achieve this in Microsoft Teams Phone when you are using Microsoft Calling Plans and don’t have a Session Border Controller (SBC) to handle complex pre-routing logic?
In this guide, we will walk you through a highly effective configuration workaround that uses native Teams features to create a PIN-protected entry point.
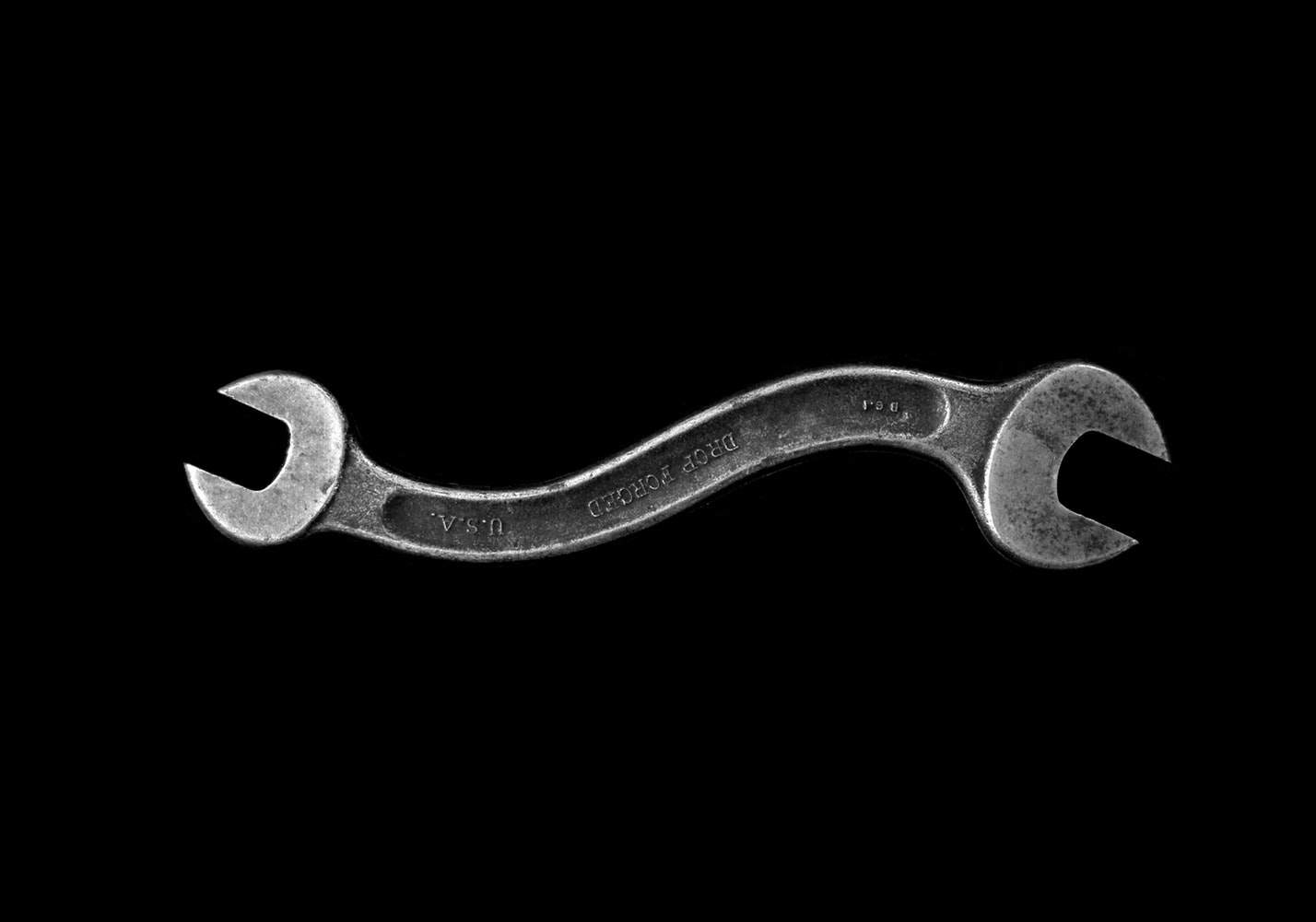
[Insert your flowchart diagram here showing PSTN call routing with PIN authentication]
🎯 The Use Case: Why Are We Doing This?
Imagine you have a dedicated VIP support hotline, an emergency IT-escalation number, or an exclusive dial-in for remote field workers. You publish a standard PSTN number, but you only want the call to ring the target team if the caller knows a specific secret code (PIN).
The Desired Flow:
- Caller dials the PSTN number.
- Caller hears an announcement: “Please enter your access code.”
- If correct: The call is routed to the target user or Call Queue.
- If incorrect / no input: The caller is told the code is invalid, and the call drops.
The Challenge: Microsoft Teams Calling Plans Limitations
If you use Direct Routing, an SBC (like AudioCodes or Ribbon) would intercept the call, ask for the PIN, verify it, and then forward the call to Teams. However, with Microsoft Calling Plans, the call goes straight into the Microsoft cloud. Microsoft Teams does not have a native “Require PIN” toggle for Auto Attendants.
The Solution: The “Dial by Extension” Hack. We will configure an Auto Attendant to ask for the PIN, but technically, Teams will be using its Dial by extension feature. The “PIN” will actually be the target user’s configured extension.
Pros and Cons of This Configuration
| ✅ Advantages (Why we do it this way) | ⚠️ Disadvantages (What you need to know) |
|---|---|
|
|
⚙️ Step-by-Step Configuration Guide
Follow these steps to set up the PIN-protected routing in your Microsoft 365 environment.
1 Prepare the Target User (Assigning the “PIN”)
First, we need to assign the secret PIN as an extension to the user who should receive the calls.
- Go to the Microsoft 365 Admin Center > Users > Active users.
- Select the target user (this user must have a Teams Phone license).
- Go to Manage contact information.
- In the Office phone field, enter a dummy number with the desired PIN as the extension. Format it strictly like this:
+10000000000;ext=8524(Assuming 8524 is your desired PIN). - Save the changes. Note: It can take up to 24 hours for the Teams directory sync to recognize the new extension, though it often takes only a few hours.
2 Create the “PIN Gateway” Auto Attendant
Now, we create the Auto Attendant that will act as the gatekeeper.
- Open the Teams Admin Center.
- Navigate to Voice > Auto attendants and click Add.
- Name it something like AA – PIN Gateway.
- Set the Operator to “Disconnect” (since we don’t want callers bypassing the PIN).
- Set the Time Zone and Language. (The language determines the voice of the default system error messages).
3 Configure Call Flow & Menu Options
This is where the magic happens. We will use the Menu Options to force the caller to interact, allowing the Directory Search to capture their DTMF (keypad) input.
- Under Call flow, choose Play menu options.
- For the audio, choose Play an audio file. Upload a professionally recorded MP3 or WAV file that says: “Welcome. Please enter your 4-digit access code to proceed. If you do not have a code, please hang up.”
- Crucial Step: Do NOT assign any keys (0-9) to routing options. Leave the dial pad assignments empty.
- Under Directory search, select Dial by extension.
What happens here? The Auto Attendant plays your custom audio. Because “Dial by extension” is enabled, it listens for keypad inputs. If the caller types 8524, the system searches the directory, finds the user from Step 1, and routes the call to them.
4 Configure Default Routing (For incorrect / no PIN)
We must define what happens if the caller just waits and presses nothing.
- Still in the Call flow section, look for the setting regarding what happens when callers don’t make a choice (Timeout).
- Set the default action to Disconnect.
What about wrong PINs? If a caller enters 1111, Teams will look for extension 1111. When it doesn’t find it, the Microsoft default voice will say “We couldn’t find a match.” After a few failed attempts, the system automatically drops the call. This fulfills the requirement that invalid codes cannot proceed.
5 Assign the PSTN Number via Resource Account
Finally, we need to make this Auto Attendant reachable from the outside world.
- Create a new Resource Account in the Teams Admin Center.
- Assign a Microsoft Teams Phone Resource Account license to it.
- Acquire a PSTN number from your Microsoft Calling Plans inventory and assign it to this Resource Account.
- Assign this Resource Account to your newly created Auto Attendant.
Conclusion
While Microsoft Teams doesn’t offer a simple “PIN toggle,” utilizing the Dial by extension feature provides a robust, zero-cost workaround for Microsoft Calling Plan users. It successfully gates a phone line behind a numeric code, ensuring only authorized callers reach your internal teams, all while keeping your infrastructure 100% in the cloud.